Security concerns stop 85% of IoT projects. Here’s how it won’t happen to you.
-
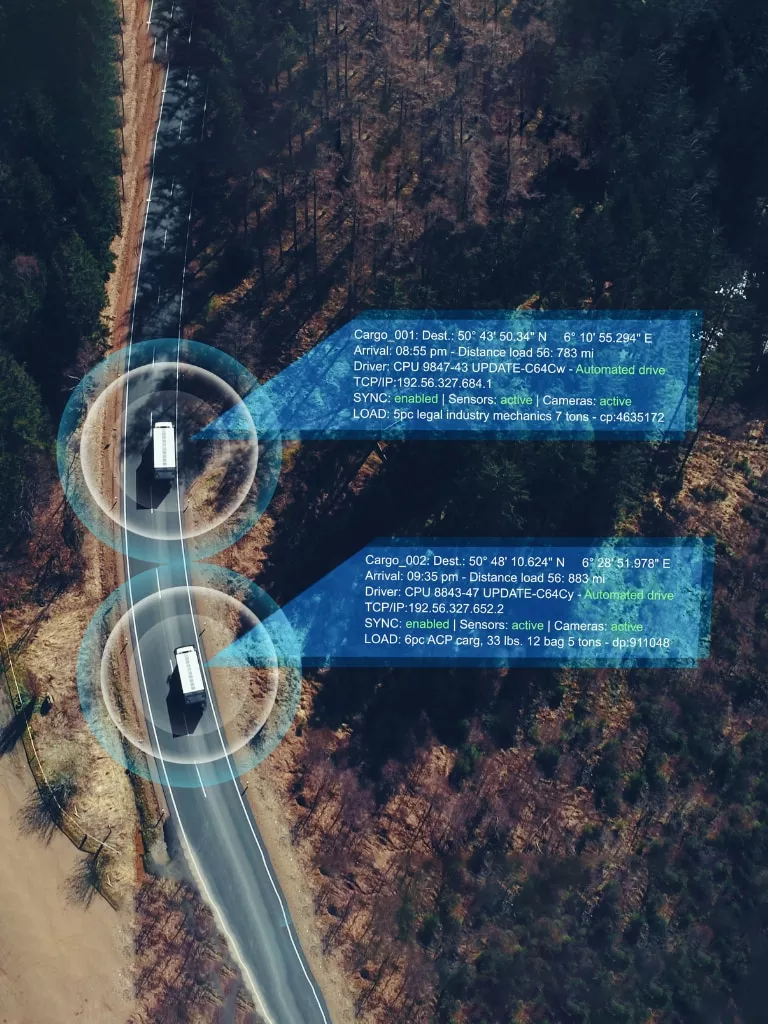
Data transport protection
End-to-end security for your IoT data as it travels to the data center through our global IPX network, avoiding the public internet.
-
Threat detection and identification
Proactively detect and identify threats across the three layers of your IoT project: device, network, and application. Let’s develop your IoT security strategy and stick to it during planning, buildout, and operation.
-
Device authentication
Ensure you don’t let unauthenticated devices into your network. Get unique IDs for your devices, which you can track in our management platform.
-
Enhance your offer
Easily integrate with solutions such as IoT Defense, Azure Sphere, and more, to further complement your offer.